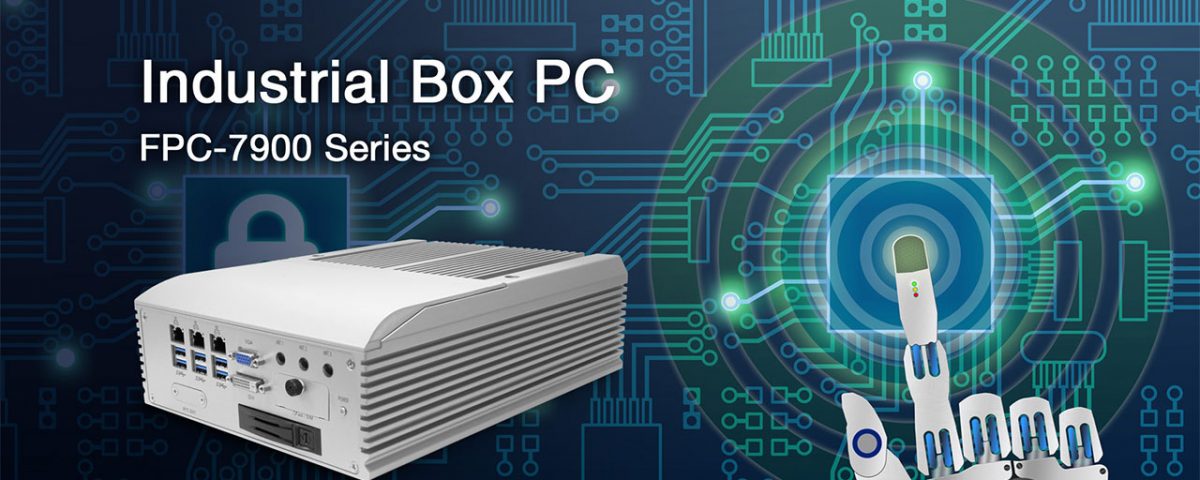
FPC-7900 Advanced Box PC with TPM 2.0
Advances in technology drive growth in all industries, yet trust in this technology can be lost in an instant if personal data and valuable information is compromised. Technology is fallible, but the risks can be minimised if effective measures are put into place.
General Data Protection Regulation (GDPR)
GDPR has come into force to better protect and enable the privacy rights of individuals. It holds every company accountable for managing and protecting the personal data of prospects, clients and employees. The majority of companies will already have systems in place, but GDPR has strict data protection guidelines that have to be adhered to.
A company will only be regarded as responsibly storing, handling, analysing and deleting data, if they can evidence that the GDPR guidelines are being followed. From May 2018, fines will be issued to companies found in breach of GDPR guidelines.
Investing in the right technology is one step to better protecting your business from attack. Many modern devices are now fitted with a Trusted Platform Module (TPM) to enhance security.
Secure TPM Enabled Technology
A Trusted Platform Module (TPM) is a chip, used in computer technology to support security and privacy at levels that software is unable to achieve. In short, TPM generates, stores and limits the use of cryptographic keys, to tightly control access to important and valuable data. TPM doesn’t operate independently; the chip has to be integrated into the system hardware in order to respond to commands and operate.
Microsoft is seen as a leader in the standardisation of TPM adoption and it is integral in Windows 10 and Windows Server 2016. They, along with many other companies, have made it easier for any computer based business to improve security. Greater protection can be achieved by upgrading to the latest TPM enabled computer technology.
TPM 2.0 – When Security is a Priority
If security is a priority in your organisation (and it should be), the latest and most secure version is TPM 2.0. This option allows for greater crypto agility and has achieved ISO/IEC 11889:2015 standards. The TPM 2.0 lock out policy has also been configured by Windows for consistent attack protection.
A significant development is that TPM 2.0 allows Trusted Computing concepts to be embedded into mobile technology. TPM 2.0 integration opens up the possibility of secure cross platform security, across a number of devices. This is a particularly important development considering the rise of flexible working. It can provide a consistent level of security despite the growing use of personal smart phones and tablets.
FPC-7900 Advanced Box PC with TPM 2.0
The integration of privacy and security features are a core component in the design of Arbor Technology’s embedded technology. This includes the adoption of TPM 2.0 in our most advanced Box PC solution; the FPC-7900.
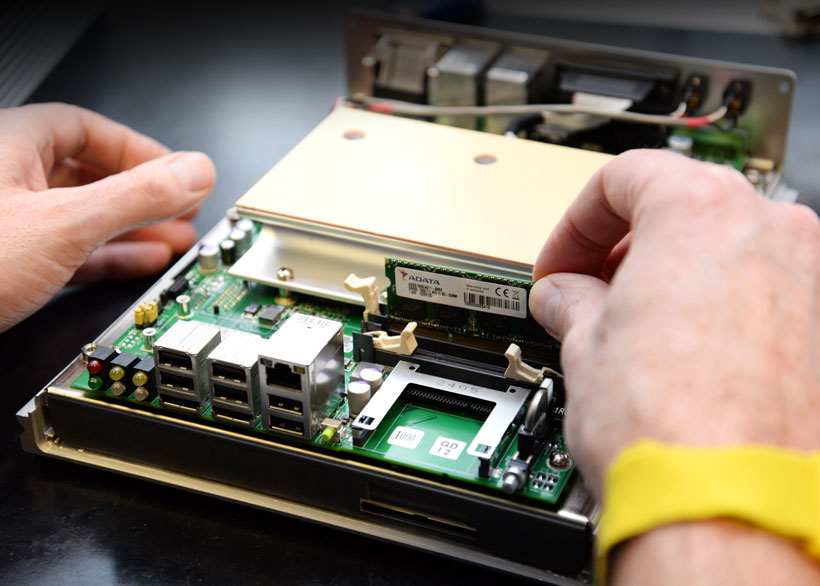
The robust, fanless FPC-7900 has been designed to meet the demands of a wide range of industrial applications. It supports Intel® Xeon® E3, 6th & 7th Generation Core™ i7/i5/i3 Processors and has considerable expansion and storage options. Our Milton Keynes workshop is fully equipped to custom configure the FPC-7900 to the specific requirements of your application.
Arbor Technology has supplied high profile companies with FPC-7900 technology and we are keen to assist others in the adoption of this advanced Box PC. The adaptable features ensure reliable performance and the integration of TPM 2.0 provides added reassurance that personal data and other critical information are protected from attack.
If you would like to discuss suitable applications for the FPC-7900 Box PC or the advantages of TPM 2.0 enabled technology,
contact our Milton Keynes team on: 01908 310100